Enterprise cloud security is no longer a technical afterthought—it is a core business requirement. As organizations shift critical operations, sensitive data, and entire infrastructures into cloud environments, the security landscape becomes more complex and significantly more exposed.
At a fundamental level, enterprise cloud security refers to the strategies, technologies, policies, and controls used to protect cloud-based systems, applications, and data from cyber threats. But this definition alone is too simplistic for modern enterprises. In reality, cloud security operates as a multi-layered defense system designed to secure dynamic, distributed, and constantly evolving environments.
Unlike traditional IT security, which relies on fixed perimeters and controlled networks, cloud environments are fluid. Resources are spun up and down on demand, users access systems from multiple locations, and applications interact through APIs across different platforms. This shift eliminates the traditional security boundary and replaces it with a model that requires continuous verification, monitoring, and adaptation.
Why Enterprise Cloud Security Matters
Ignoring cloud security is not a passive decision—it is an active risk. A single misconfiguration in a cloud environment can expose thousands of assets simultaneously, making enterprises high-value targets for cybercriminals.
Modern organizations manage massive volumes of sensitive data, including customer information, financial records, and proprietary systems. When this data is compromised, the consequences extend beyond financial loss. Regulatory penalties, operational disruption, and long-term reputational damage can follow.
Research consistently shows that misconfigurations and over-permissioned identities are among the leading causes of cloud breaches. These are not advanced attacks—they are preventable failures. Yet at enterprise scale, even small mistakes can escalate into major incidents.
The growing adoption of artificial intelligence in cloud environments introduces an additional layer of risk. AI models, data pipelines, and automated systems create new attack surfaces that must be secured. Many organizations are deploying AI faster than they are securing it, creating a gap that attackers can exploit.
How Enterprise Cloud Security Works
Enterprise cloud security operates on a shared responsibility model. This model defines the division of security responsibilities between cloud service providers and the organizations that use their services.
Cloud providers are responsible for securing the core infrastructure layer, including physical data centers, hardware, networking, and virtualization that power the cloud environment.This includes physical data centers, servers, networking components, and the virtualization layer. In simple terms, they secure the cloud itself.
Enterprises, on the other hand, are responsible for securing everything within the cloud. This includes data, applications, user access, configurations, and operating systems. This is often referred to as securing what is in the cloud.
The problem is not the model itself—it’s misunderstanding it. Many organizations assume that cloud providers handle most security responsibilities, which leads to gaps in protection. In reality, most breaches occur in areas that fall under the customer’s control.
Effective cloud security requires continuous monitoring of configurations, user activity, and system behavior. It also depends heavily on identity management, access control, and automated threat detection systems that can respond in real time.
Cloud Deployment Models and Security Differences
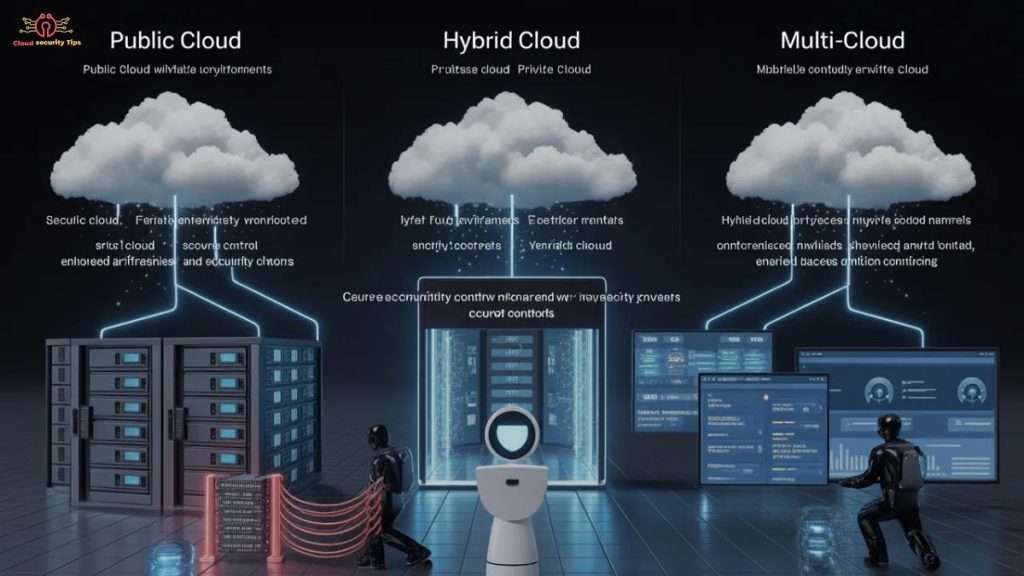
Enterprise cloud environments are not uniform. Public, private, and hybrid cloud models each introduce different security considerations.
Public cloud platforms offer scalability and cost efficiency but operate on shared infrastructure. While providers implement strong isolation mechanisms, organizations must carefully manage configurations and access controls to avoid exposure.
Private clouds provide dedicated infrastructure, offering greater control and customization. This makes them suitable for industries with strict compliance requirements. However, this control comes with increased responsibility for maintenance and security management.
Hybrid and multi-cloud environments combine multiple platforms, allowing organizations to balance performance, cost, and security. However, they also introduce complexity. Managing consistent security policies across different providers can create visibility gaps and increase the risk of misconfigurations.
Core Components of Enterprise Cloud Security
Enterprise cloud security is built on multiple interconnected components that work together to protect systems and data.
Identity and access management is one of the most critical elements. It controls who can access resources and what actions they can perform. Weak identity controls are one of the fastest ways to compromise a cloud environment.
Data protection focuses on securing sensitive information through encryption, masking, and tokenization. Data must be protected both when stored and when transmitted between systems.
Network security ensures that communication between cloud resources is protected. Segmentation, firewalls, and secure access controls prevent attackers from moving laterally within the environment.
Workload and application security protect the systems running in the cloud. This includes virtual machines, containers, and serverless applications, all of which require continuous monitoring and vulnerability management.
Common Enterprise Cloud Security Threats
Cloud environments face a wide range of threats, many of which exploit basic weaknesses rather than advanced vulnerabilities.
Misconfigurations remain the most common issue. Exposed storage buckets, open ports, and overly permissive access settings can unintentionally make sensitive data public.
Credential theft is another major risk. Attackers use phishing, leaked credentials, and brute force attacks to gain access. Once inside, they often escalate privileges and move across systems.
Data breaches and leaks occur when sensitive information is accessed or extracted without authorization. These incidents are often linked to poor access controls or insecure APIs.
Advanced persistent threats represent more sophisticated attacks, where attackers infiltrate systems and remain undetected for extended periods.
The rise of AI-driven environments has also introduced new risks. AI models and data pipelines can be manipulated, creating vulnerabilities that did not exist in traditional systems.
Key Challenges in Enterprise Cloud Security
The biggest challenge in enterprise cloud security is not technology—it is complexity.
Large organizations operate across multiple cloud platforms, regions, and services. This creates fragmented environments where maintaining visibility becomes difficult. Without clear visibility, identifying risks and responding to threats becomes nearly impossible.
Scale amplifies every issue. A misconfiguration that affects one system in a small environment can impact thousands in an enterprise setting.
Ownership is often unclear. Security responsibilities are divided across multiple teams, including DevOps, IT, and compliance. This fragmentation creates gaps that attackers can exploit.
Compliance adds another layer of difficulty. Regulations require strict control over data and systems, and maintaining compliance in dynamic cloud environments requires continuous monitoring and documentation.
The rapid adoption of AI introduces what can be described as “shadow AI”—systems deployed without proper oversight. This creates blind spots similar to the early days of cloud adoption.
Benefits of Enterprise Cloud Security
When implemented effectively, enterprise cloud security does more than protect systems—it enables business growth.
It allows organizations to scale securely, adapting to changing demands without compromising protection. Security systems can expand alongside infrastructure, maintaining consistent coverage.
Cost efficiency improves as automation reduces the need for manual processes. Security-as-a-service models also eliminate the need for large upfront investments in hardware.
Threat detection becomes faster and more accurate. AI-driven systems analyze behavior patterns and identify anomalies before they escalate into serious incidents.
Strong security also supports compliance efforts, helping organizations meet regulatory requirements and maintain trust with customers and partners.
Enterprise Cloud Security Best Practices
Effective cloud security requires a proactive and strategic approach.
Zero trust architecture is now a core security principle, where no user or system is trusted by default and every access request must be continuously verified.. Instead of assuming trust within the network, every request is verified based on identity, context, and risk.
Identity management should follow the principle of least privilege, ensuring users only have access to the resources they need. Permissions must be continuously reviewed, monitored, and dynamically adjusted to prevent privilege creep and unauthorized access.
Security must be integrated into development processes. Identifying vulnerabilities during development is far more effective than addressing them after deployment.
Automation plays a critical role. Real-time monitoring, automated alerts, and rapid response mechanisms allow organizations to react quickly to threats.
AI governance is becoming increasingly important. Organizations must track and secure AI systems just as they would any other critical asset.
Enterprise Cloud Security Architecture
A strong security architecture provides the foundation for protecting cloud environments.
Layered security ensures that multiple controls protect each component of the systemEven if one security layer is compromised, additional layers continue to provide protection and limit the impact of the breach.
Secure network design includes segmentation and isolation, limiting the impact of potential breaches. Attackers should not be able to move freely across systems.
Integration with existing IT infrastructure ensures consistency across environments. Cloud security should align with broader cybersecurity strategies rather than operate independently.
Compliance and Regulatory Requirements
Compliance is a major driver of enterprise cloud security.
Regulations such as GDPR, HIPAA, and PCI DSS require organizations to implement strict controls over data protection and access. Failure to comply with regulatory requirements can lead to severe financial penalties, legal consequences, and reputational damage.
Data governance ensures that organizations understand where their data is stored, how it is used, and who can access it. This is essential for both security and compliance.
Automating compliance processes allows organizations to maintain continuous alignment with regulatory requirements, reducing the risk of human error.
How to Implement Enterprise Cloud Security
Implementing enterprise cloud security requires a structured and strategic approach.
Organizations must begin by assessing their current environment to identify vulnerabilities and gaps. This includes reviewing configurations, access controls, and monitoring systems.
Selecting the right tools is critical. Solutions should provide visibility across all cloud environments, support automation, and integrate with existing systems.
Building a security-first culture ensures that employees understand their role in protecting the organization. Human error remains one of the biggest risks, and training is essential to reduce it.
How to Choose an Enterprise Cloud Security Solution
Choosing the right solution goes beyond feature comparison and requires evaluating scalability, security depth, integration capability, and long-term reliability.
Organizations should focus on platforms that provide unified visibility, risk prioritization, and automated remediation. Tools that operate in isolation often create more problems than they solve.
Scalability is essential. The solution must be able to handle growing environments without sacrificing performance.
Vendor reliability and ongoing support are also critical factors. Security is not static, and solutions must evolve alongside emerging threats.
Emerging Trends in Enterprise Cloud Security
Cloud security is evolving rapidly, driven by new technologies and changing threat landscapes.
Artificial intelligence is transforming both attack and defense strategies. While AI improves threat detection and response, it also introduces new vulnerabilities that must be managed.
Cloud-native security platforms are becoming more popular, offering integrated solutions that combine multiple security functions into a single system.
Automation is advancing to the point where systems can detect and respond to threats without human intervention, reducing response times and limiting damage.
Zero trust continues to evolve, becoming more deeply integrated into cloud environments and identity systems.
Final Insight
Enterprise cloud security is not a single solution or tool—it is a continuously evolving strategy. Organizations that treat it as a one-time implementation will fall behind.
The real challenge is not adopting cloud technologies, but securing them at scale. Those that succeed are not necessarily the ones with the most tools, but the ones with the clearest visibility, strongest processes, and most disciplined approach to security.
If you approach cloud security as a checklist, you will miss critical gaps. If you approach it as an ongoing system that adapts with your environment, you build resilience.
That distinction is what separates organizations that experience breaches from those that prevent them.
FAQs
What is enterprise cloud security in simple terms?
Enterprise cloud security protects data, applications, and infrastructure in cloud environments using policies, tools, and access controls.
What are the main risks in enterprise cloud security?
The biggest risks include misconfigurations, over-permissioned access, data breaches, insecure APIs, and credential theft.
Who is responsible for cloud security—the provider or the company?
Cloud providers secure the infrastructure, while companies are responsible for securing their data, users, applications, and configurations.
What is the most important component of cloud security?
Identity and access management (IAM) is critical, as it controls who can access systems and prevents unauthorized entry.
What is the best strategy for enterprise cloud security?
The most effective strategy includes zero trust architecture, least privilege access, continuous monitoring, and automated threat detection.

