Cloud adoption has become the foundation of modern businesses, but it has also introduced one of the fastest-growing attack surfaces in cybersecurity. Most breaches today do not happen because cloud systems are inherently weak—they happen because of poor identity control, misconfigurations, and lack of visibility.
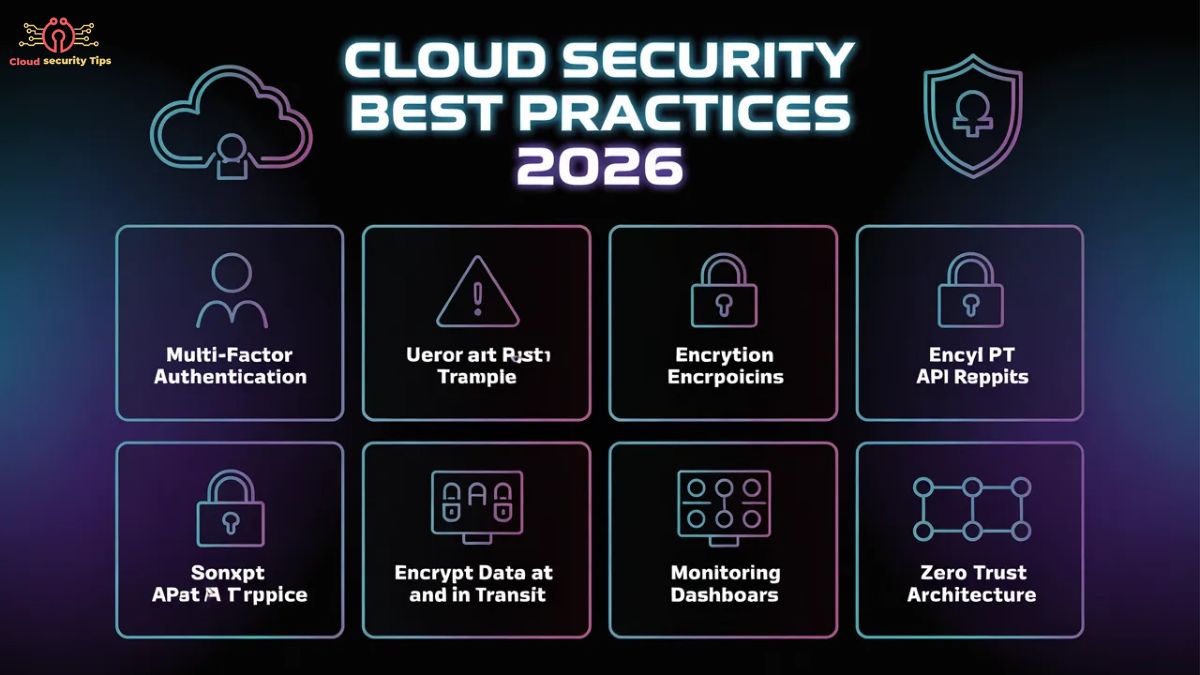
This guide breaks down the most critical cloud security practices for 2026 in a structured, practical format that focuses on real-world implementation.
What Makes Cloud Security Difficult Today?
Rapidly Changing Environments
Cloud systems evolve constantly. New services, APIs, and workloads are deployed daily, often without centralized oversight. This speed creates security gaps faster than teams can detect them.
Misconfiguration Risk
One of the biggest issues in cloud security is not hacking—it is simple configuration errors. A single exposed storage bucket or overly permissive role can lead to full data exposure.
Shared Responsibility Confusion
Cloud providers secure infrastructure, but users are responsible for configurations, access control, and data protection. Misunderstanding this split is one of the main reasons breaches occur.
Identity and Access Security: The First Line of Defense

Why Identity Matters Most
Most cloud attacks begin with stolen credentials or excessive permissions. Once an attacker gains access, they don’t break systems—they log in normally.
Enforcing Strong Authentication
Multi-factor authentication is no longer optional. Every privileged account must use MFA or passwordless authentication such as passkeys to prevent credential-based attacks.
Least Privilege Access Control
Every user and system should only have the minimum permissions required. Over-permissioned accounts dramatically increase the damage of a breach.
Managing IAM Consistency
In multi-cloud environments, inconsistent identity policies create blind spots. Standardizing IAM rules across platforms ensures predictable and secure access behavior.
Removing Risky Credentials
Hard-coded keys and unused accounts are silent security risks. Credentials should be stored in secure vault systems and rotated regularly, while inactive accounts should be disabled automatically.
Cloud Configuration Security and Posture Management

The Hidden Risk of Misconfiguration
Most cloud breaches are not sophisticated attacks—they are preventable configuration mistakes. These errors often go unnoticed until damage is already done.
Continuous Monitoring with CSPM
Cloud Security Posture Management tools provide real-time visibility into risky configurations such as open ports, public storage, or weak access policies.
Preventing Public Exposure
Accidentally exposing internal resources to the internet is still one of the most common causes of data leaks. Regular exposure audits are essential.
Importance of Regular Security Audits
Even with automation, manual reviews are necessary to identify logic errors and complex misconfigurations that tools may miss.
Data Protection and Encryption Strategy
Securing Data at Rest and in Transit
Encryption ensures that even if data is intercepted or exposed, it remains unreadable without the correct keys.
Data Classification and Governance
You cannot secure what you cannot identify. Classifying sensitive data helps apply the correct level of protection based on risk.
Strong Key Management Practices
Encryption is only as secure as the way its keys are managed, since improper handling of keys often creates the most vulnerable point in cloud security systems.
Backup and Recovery Readiness
Backups are not enough on their own. Organizations must regularly test recovery processes to ensure data can actually be restored during incidents.
Securing Cloud Workloads, Networks, and APIs

Workload Protection in Dynamic Environments
Cloud workloads are frequently created and destroyed. Each workload must be secured individually with trusted images and runtime protection.
Network Hardening and Segmentation
Open ports and unrestricted traffic paths allow attackers to move laterally across systems. Network segmentation limits this movement.
API Security Risks
APIs are one of the most targeted components in cloud environments. Weak authentication or missing rate limits can expose critical systems.
Protecting Containers and Serverless Systems
Modern cloud-native applications require isolated security controls because they run in highly dynamic and distributed environments.
Monitoring, Detection, and Incident Response
The Importance of Centralized Logging
Without centralized logs, investigating incidents becomes slow and unreliable. Unified logging improves visibility and response time.
Continuous Threat Monitoring
Cloud environments operate 24/7, so security monitoring must also be continuous to detect suspicious behavior early.
Automating Compliance Checks
Compliance should not be a manual process. Automated systems ensure configurations remain aligned with security and regulatory standards.
Incident Response Preparedness
Security teams must regularly simulate real-world attacks. Without practice, response speed and coordination break down during actual incidents.
Advanced Cloud Security Practices for 2026
Zero Trust Architecture
No user or system should be trusted by default, and every request must be continuously verified regardless of identity or location.
External Threat Intelligence
Modern attacks often originate outside the organization. Monitoring leaked credentials and exposed assets provides early warning signals.
Securing CI/CD Pipelines
Many modern breaches originate from development pipelines. Protecting code repositories and deployment systems is now essential.
Policy-as-Code Enforcement
Security rules should be automated and enforced through code to eliminate human error and inconsistency.
Final Reality Check
If your cloud security strategy is only focused on firewalls or encryption, you are already behind. Modern cloud attacks target identity systems, misconfigurations, and exposed APIs—not perimeter defenses.
Real security comes from consistency, visibility, and strict access control across every layer of your cloud environment.
FAQ
1. What is cloud security in simple terms?
Cloud security is the practice of safeguarding cloud-based data, applications, and infrastructure using a combination of security policies, technologies, and controls designed to prevent unauthorized access and cyber threats.
2. Why is cloud security important in 2026?
Cloud security is critical in 2026 because most attacks now focus on weak identities, misconfigured cloud services, and poor access control rather than traditional system vulnerabilities.
3. What is the biggest risk in cloud security?
The biggest risks in cloud security are compromised identities and configuration errors, such as excessive permissions or publicly exposed cloud resources.
4. What is the principle of least privilege?
The principle of least privilege is a security model that restricts access so users and systems only receive the minimum permissions required to perform their functions, reducing potential damage from breaches.
5. How can companies improve cloud security quickly?
By enabling MFA, fixing misconfigurations, encrypting data, and continuously monitoring cloud activity for unusual behavior.

1 thought on “Cloud Security 2026: Best Practices & Protection Guide”