Phone number spoofing is one of the most widespread communication fraud techniques in modern digital scams. It works by manipulating caller ID information so that the receiver sees a trusted or familiar number instead of the real origin of the call. This single trick is responsible for a large portion of financial fraud, impersonation scams, and social engineering attacks worldwide.
The problem is not just technical—it is psychological. Spoofing works because people trust what they see on their screen more than what they hear on the call. That trust gap is what attackers exploit.
What Phone Number Spoofing Actually Is
Phone number spoofing is the process of disguising the original phone number of a caller and replacing it with a different number that appears on the recipient’s caller ID. In most cases, the number shown looks local, official, or familiar, which increases the chance that the call will be answered.
This technique is commonly used in both legitimate and illegal contexts. Businesses sometimes use controlled caller ID systems for branding or customer support consistency. However, criminals use the same mechanism to impersonate banks, government agencies, delivery companies, or tech support teams.
The core idea is simple: replace identity at the point of contact.
How Phone Number Spoofing Works Technically
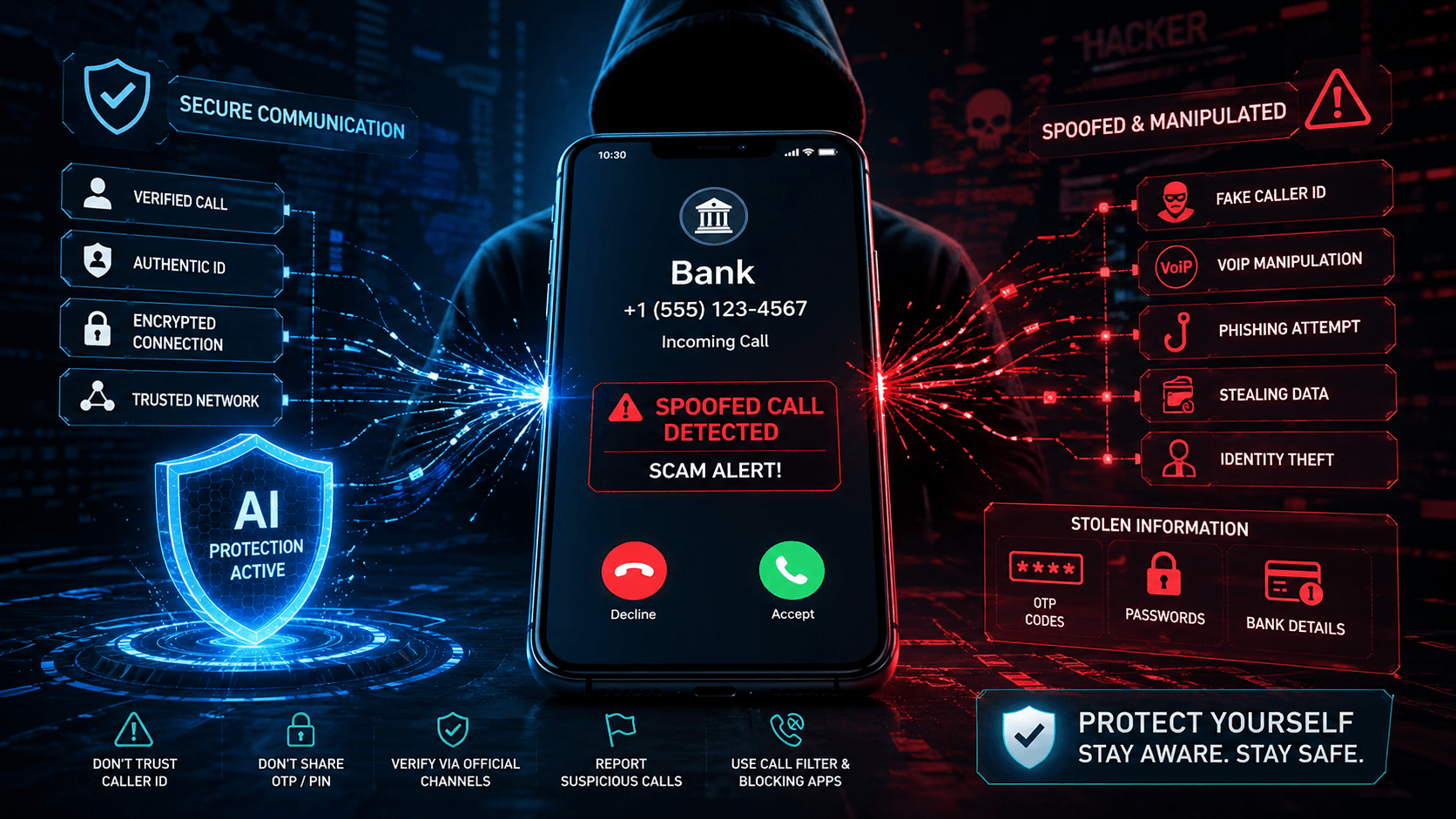
At a technical level, spoofing is possible because the telephone network does not always verify whether the caller ID information is authentic. When a call is placed through modern systems such as VoIP (Voice over Internet Protocol), the caller can embed any number they want into the outgoing signal.
VoIP services act as the primary gateway for spoofing. Instead of routing calls through traditional telecom infrastructure, VoIP converts voice into digital data packets that travel over the internet. During this process, caller ID metadata can be modified before reaching the recipient.
Another method involves third-party service providers that allow users to set custom caller IDs. While these services can have legitimate uses, they are frequently abused when weak verification systems exist.
More advanced techniques exist as well, where attackers use system-level manipulation or outdated telecom protocols to inject false caller ID data directly into the network flow. These methods are more complex but demonstrate that spoofing is not limited to simple apps or tools.
The important takeaway is this: spoofing does not “hack” your phone—it exploits weaknesses in the communication infrastructure itself.
Why Scammers Use Spoofing in Fraud Attacks
Spoofing is not used randomly. It is a strategic tool designed to increase response rates and reduce suspicion.
One of the strongest advantages for scammers is trust manipulation. If a call appears to come from a bank, government office, or local number, the victim is far more likely to answer and comply. This reduces the need for attackers to convince people to engage—they already have attention.
Another major reason is geographic masking. Scammers often operate internationally. Spoofing allows them to appear as if they are calling from the same country, city, or even area code as the victim. This significantly improves success rates.
It also supports authority impersonation, where attackers pretend to be officials or service providers. Once authority is established, victims are pressured into sharing sensitive information such as OTP codes, passwords, or banking details.
In most cases, spoofing is not the scam itself—it is the entry point for a larger fraud operation.
How Scam Calls Using Spoofing Actually Work
Spoofed scam calls usually follow a predictable psychological pattern. First, the victim receives a call that appears legitimate. The caller often introduces urgency, claiming issues such as suspicious bank activity, unpaid taxes, account suspension, or package delivery problems.
Once the emotional pressure is established, the attacker moves toward data extraction. This can include verification codes, login credentials, or direct financial transfers.
Some advanced scams involve multi-step manipulation, where the victim is transferred between “departments” or asked to verify identity through repeated actions. Each step is designed to build trust while increasing control.
What makes this dangerous is not the technology itself, but the structured psychological manipulation layered on top of it.
How to Recognize a Spoofed Call
Spoofed calls are not always obvious, but they often share behavioral patterns.
One of the most common indicators is unnatural urgency. Legitimate institutions rarely demand immediate action over a phone call without prior written communication. If a caller is pushing fast decisions, that is a warning sign.
Another signal is unexpected contact. If you receive a call from a bank or agency you were not actively interacting with, it should be treated with caution.
Requests for sensitive data are another clear indicator. No legitimate organization asks for OTP codes, passwords, or full banking credentials over a call.
Even when the number looks familiar, that alone cannot be trusted. Caller ID is no longer a reliable identity signal in modern communication systems.
Risks and Consequences of Phone Number Spoofing
The impact of spoofing extends beyond individual scams.
Financial loss is the most immediate consequence. Victims often transfer money voluntarily under deception, making recovery difficult.
Identity theft is another major risk. Once personal information is exposed, attackers can open accounts, access services, or conduct further fraud in the victim’s name.
There is also a broader social impact: erosion of trust in phone communication. As spoofing becomes more common, people become hesitant to answer legitimate calls, which affects businesses, emergency communication, and customer service systems.
Over time, this creates a communication environment where trust must be constantly verified instead of assumed.
Is Phone Number Spoofing Legal?
Spoofing itself is not always illegal. The legality depends entirely on intent and usage.
In legitimate cases, businesses may use controlled caller ID systems to display customer service numbers or maintain brand consistency. These uses are generally allowed when transparent and compliant with telecom regulations.
However, spoofing becomes illegal when it is used to deceive, impersonate, or commit fraud. This includes pretending to be government agencies, banks, or other trusted entities for financial or personal gain.
Different countries enforce these rules differently, but most regulatory frameworks now treat fraudulent spoofing as a serious cybercrime.
How to Protect Yourself from Spoofing Attacks
Protection against spoofing requires behavior changes, not just technology.
The most important rule is not to trust caller ID alone. Identity must be verified through independent channels such as official websites or known contact numbers.
Sensitive information should never be shared over unsolicited calls. This includes passwords, OTPs, PINs, and banking details.
Using call filtering and spam detection tools can reduce exposure, but they are not perfect. They should be treated as a support layer, not a full solution.
Awareness is the strongest defense. Understanding how manipulation works reduces the likelihood of emotional decision-making during a scam attempt.
How to Stop Spoofed Calls and Reduce Exposure
Stopping spoofed calls completely is not realistic because the attack happens at the network level. However, exposure can be significantly reduced.
Mobile operating systems now include built-in spam detection features that identify suspicious call patterns. Enabling these features helps filter high-risk calls.
Third-party call-blocking applications also provide additional protection by maintaining large databases of reported scam numbers.
On a behavioral level, not answering unknown numbers consistently reduces targeting over time. Scammers often prioritize active numbers that respond.
In severe cases, users may need to contact their telecom provider for enhanced filtering options or number protection services.
Spoofed Call Alert: What You Should Do Right Now
If you suspect a spoofed call, the safest action is immediate disengagement. Continuing the conversation increases risk, even if no information has been shared yet.
Blocking the number helps reduce repeat contact, although spoofed numbers may change frequently.
Reporting the call to relevant authorities or telecom providers contributes to broader scam detection systems.
If any personal or financial information was shared, account monitoring should begin immediately to detect unauthorized activity.
Future of Phone Number Spoofing and Call Security
Spoofing is evolving alongside communication technology. One of the emerging threats is AI-generated voice scams, where attackers can replicate voices to increase credibility.
Another development is deepfake-style audio manipulation combined with spoofed caller IDs, creating highly convincing impersonation attacks.
To counter this, telecom providers are gradually implementing verification protocols such as STIR/SHAKEN, which aim to authenticate caller identity at the network level. While these systems are improving, global adoption is still uneven.
Artificial intelligence is also being used defensively to detect abnormal calling patterns and flag potential fraud in real time.
The future of call security will likely rely on layered verification systems rather than a single protective method.
Final Perspective
Phone number spoofing is not a simple scam trick—it is a structural weakness in global communication systems combined with psychological manipulation techniques.
The real danger is not the technology itself but the assumption that caller ID equals identity. That assumption is outdated.
Protection requires a shift in mindset: every unexpected call must be treated as unverified until proven legitimate.
Once that principle is applied consistently, the effectiveness of spoofing-based scams drops significantly.
FAQs
1. What is phone number spoofing?
Phone number spoofing is when a caller hides their real number and makes a different number appear on your caller ID.
2. Can spoofed calls be trusted if they look local?
No. Even local-looking numbers can be faked, so caller ID alone is not reliable.
3. Is phone number spoofing illegal?
It is legal only in controlled or business use cases, but illegal when used for fraud or impersonation.
4. How can I know if a call is spoofed?
If the caller pressures you, asks for sensitive data, or claims urgent action, it is likely a scam.
5. Can I completely stop spoofed calls?
No system can fully stop them, but spam filters, call blocking, and careful behavior can reduce them significantly.

2 thoughts on “Phone Number Spoofing: How Scammers Trick You & How to Stop It”