Understanding the Role of IP Addresses in Modern Digital Infrastructure
An IP address is not just a technical identifier; it is the foundation of how every device communicates across the internet. Every request you send, every website you load, and every server interaction depends on a structured addressing system that allows data to move across networks without confusion. In modern networking, IP addresses act as routing identities that ensure packets of information reach the correct destination.
Within this system, IPv4 remains one of the most widely used formats despite the gradual transition toward IPv6. IPv4 addresses follow a strict numerical structure, and any deviation from this structure results in invalid recognition by network systems. This is where formats like 185.63.2253.200 become important for analysis, not because they are functional, but because they highlight validation rules and system behavior when incorrect data appears.
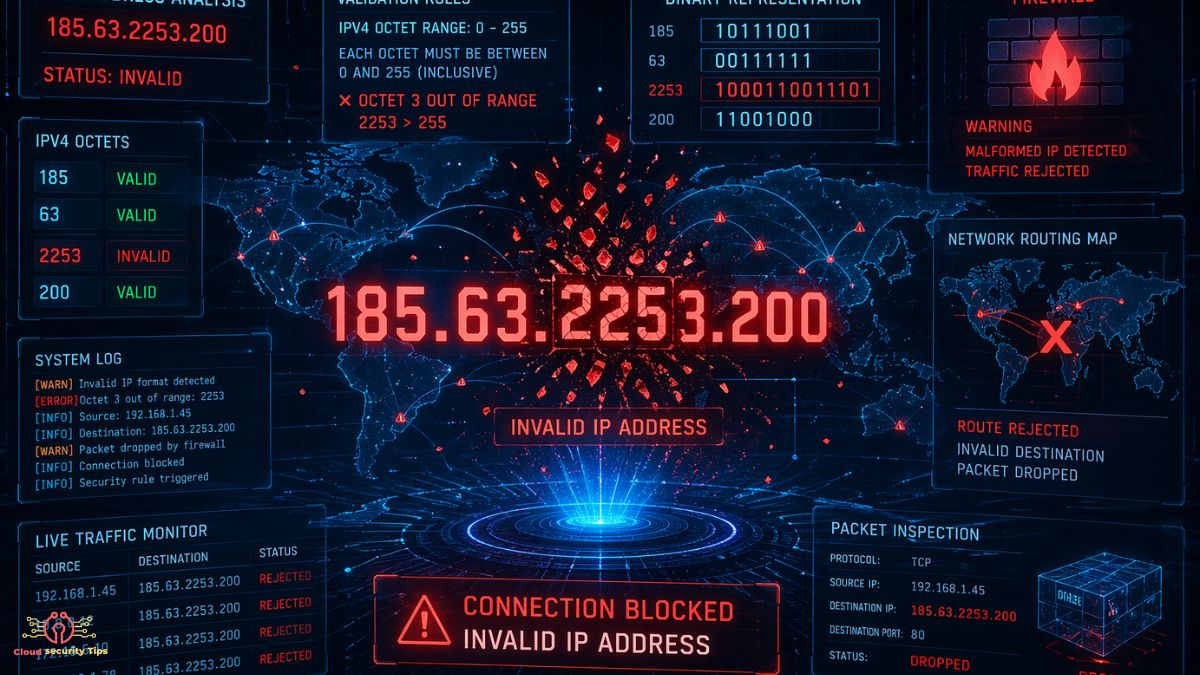
Why 185.63.2253.200 Is an Invalid IP Address
At first glance, 185.63.2253.200 appears to follow the IPv4 pattern of four numerical segments separated by dots. However, structural compliance does not guarantee validity. IPv4 addresses are restricted to values between 0 and 255 in each segment. The third segment in this case, “2253”, exceeds this limit, making the entire address invalid in any standard networking environment.
This type of invalid format usually appears due to human error, system misconfiguration, or corrupted data processing. In real-world systems, invalid IP entries are not ignored; they are flagged, logged, and often filtered out during validation processes. Understanding why this format fails is essential for developers, system administrators, and cybersecurity engineers who rely on accurate network data.
From an SEO semantic perspective, this topic connects strongly with concepts such as IP validation rules, network data integrity, IPv4 constraints, and error detection in packet routing systems.
Structural Breakdown of IPv4 Addressing and Validation Rules
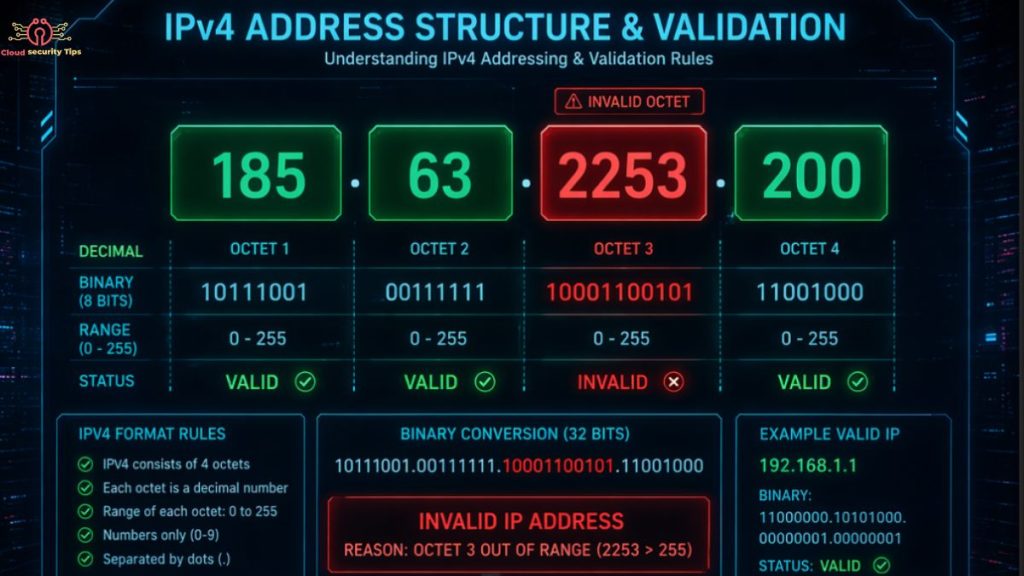
IPv4 addresses are built on a 32-bit numerical system divided into four octets. Each octet must remain within a strict numeric range to ensure compatibility across global routing systems. When an address like 185.63.2253.200 appears, it violates the core constraint of octet boundaries.
Network systems do not interpret IP addresses as simple text strings. Instead, they convert them into binary representations for routing efficiency. When a segment exceeds its allowable range, the conversion process fails, and the address is rejected during validation.
This validation layer is critical because it prevents malformed data from entering routing tables, which could otherwise disrupt communication systems or lead to misdirected traffic flows.
Related semantic clusters in this context include IPv4 structure rules, binary conversion of IP addresses, subnet boundaries, and network packet routing integrity.
How Invalid IP Addresses Appear in Real-World Systems
Invalid IP formats such as 185.63.2253.200 often originate from non-malicious sources. In most cases, they are the result of data entry mistakes, software parsing errors, or improperly formatted logs. In large-scale systems that handle millions of requests per second, even small formatting inconsistencies can propagate into analytics systems if not properly sanitized.
Another common source is application-level logging. When systems attempt to record network activity without strict validation rules, malformed entries can be stored in logs. Over time, these entries create noise in datasets and reduce the accuracy of network analysis tools.
This is why modern infrastructure increasingly relies on automated validation pipelines that clean and normalize IP data before it is stored or processed further.
The Importance of IP Address Validation in Cybersecurity

IP validation is not just a technical requirement; it is a security layer. Invalid or malformed IP addresses can sometimes be used as part of obfuscation techniques or injected into logs to hide malicious activity. While 185.63.2253.200 itself is not harmful, its presence in a dataset could indicate either system corruption or intentional manipulation of log data.
Security systems depend on clean input to detect anomalies. When invalid IPs are present, they can distort threat detection models or create false positives in monitoring tools. This is particularly important in intrusion detection systems, firewall logging, and traffic analysis platforms.
Semantic clusters relevant here include cybersecurity log integrity, anomaly detection in network traffic, IP-based threat filtering, and data sanitization in security pipelines.
IP Address Validation Mechanisms and Technical Enforcement
Modern systems use multiple layers of validation to ensure IP correctness. At the application level, validation checks ensure that input data conforms to IPv4 or IPv6 standards before processing. At the network level, routing protocols inherently reject invalid addresses during packet forwarding.
Programming languages and frameworks also provide built-in validation libraries that enforce correct formatting rules. These validation mechanisms help prevent invalid data like 185.63.2253.200 from entering production systems.
In high-scale environments, validation is often combined with regex pattern matching, numeric range enforcement, and schema-based data validation systems. This multi-layered approach ensures that malformed data is filtered out as early as possible.
Public vs Private IP Address Context
Understanding invalid IP formats also requires understanding the difference between public and private IP spaces. Public IP addresses are globally routable and must follow strict allocation rules governed by internet authorities. Private IP addresses, on the other hand, are used within internal networks and follow reserved ranges.
Even though 185.63.2253.200 does not fall into either category due to its invalid structure, its analysis helps reinforce how strict these systems are. Any deviation from allowed ranges immediately breaks classification rules, which is why validation systems are essential for maintaining network order.
IP Address Errors in Data Analytics and Logging Systems
In large-scale analytics systems, IP addresses are often used to track user behavior, detect fraud patterns, and analyze traffic sources. When invalid IP addresses appear, they introduce noise into datasets, reducing the accuracy of insights.
For example, a single malformed IP entry can skew geographic mapping systems or misclassify traffic sources. This is why data pipelines increasingly include normalization steps that remove or correct invalid network identifiers before analysis.
Semantic relevance here includes log normalization, data cleaning in analytics pipelines, traffic source attribution, and IP-based behavioral analysis.
Future of IP Addressing and System Validation
The future of IP addressing is moving toward more structured and intelligent systems. IPv6 adoption is increasing globally, offering a vastly larger address space and improved hierarchical routing. At the same time, AI-driven network monitoring systems are beginning to play a role in detecting anomalies in real time.
In this future environment, invalid IP detection will become more automated and predictive. Instead of simply rejecting malformed entries, systems will classify them based on origin, frequency, and context to identify potential configuration issues or security threats.
This evolution connects strongly with semantic trends like intelligent network validation, AI-based traffic monitoring, and next-generation internet infrastructure.
Conclusion: Why 185.63.2253.200 Matters in Technical Analysis
Although 185.63.2253.200 is not a valid IP address, its value lies in what it represents within networking systems. It highlights the importance of strict formatting rules, validation mechanisms, and data integrity in modern digital infrastructure.
In real-world environments, even a single malformed IP can affect logs, analytics, and security systems if not properly handled. Understanding why such formats fail is essential for building robust, secure, and scalable network architectures.
Ultimately, IP validation is not a minor technical detail—it is a foundational requirement for maintaining trust, accuracy, and stability across global internet systems.
FAQ
1. Is 185.63.2253.200 a valid IP address?
No, it is not valid because the third segment (2253) exceeds the IPv4 limit of 0–255.
2. Why is 185.63.2253.200 considered invalid?
It violates IPv4 rules since each octet must be between 0 and 255, and 2253 is out of range.
3. What happens when an invalid IP is used in a system?
Systems reject it during validation, and it may be logged as an error or ignored.
4. Can invalid IP addresses affect security systems?
Yes, they can create noise in logs and reduce accuracy in monitoring and threat detection systems.
5. How are IP addresses validated in modern systems?
They are checked using range rules, format validation, and automated libraries or network tools.